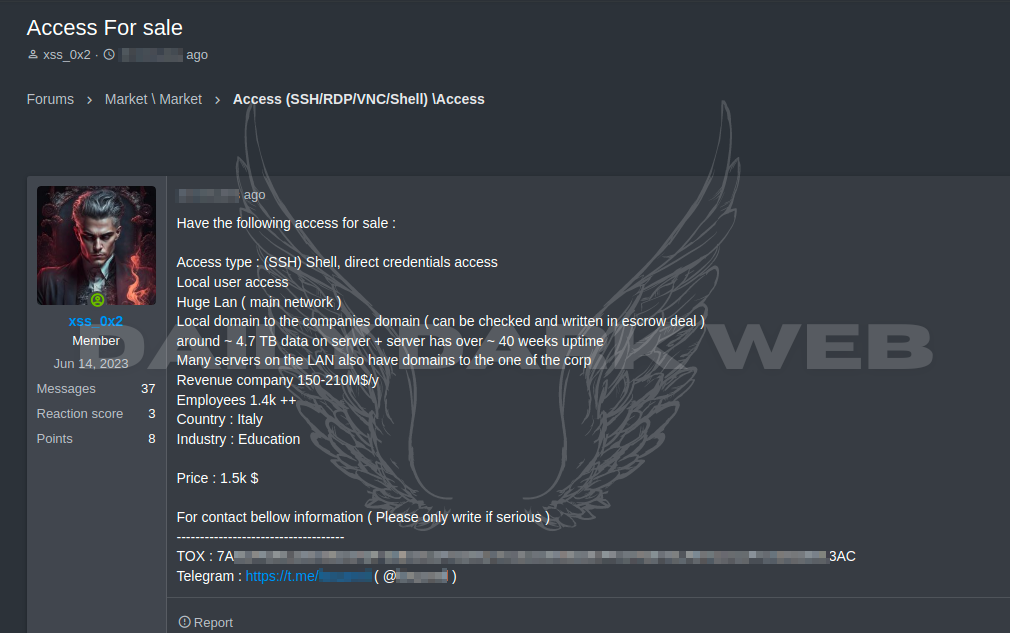
A threat actor offers unauthorized SSH access to an Italian education sector company, enticing buyers with the promise of extensive data. The threat actor claims to possess access to approximately 4.7TB of data stored on the server, which boasts over 40 weeks of uninterrupted uptime. With access types including direct credentials and local user privileges, this offer extends to a vast LAN network with connections to multiple servers. The targeted company, with an annual revenue ranging from $150 to $210 million, employs over 1.4k individuals. Situated in Italy, this breach poses significant concerns for the education industry’s cybersecurity landscape.
With the unauthorized SSH access to the Italian education sector company, the threat actor can potentially engage in various malicious activities, including:
Data Theft: The threat actor can extract sensitive information stored on the company’s servers, such as student records, financial data, intellectual property, and employee details.
Espionage: Access to the company’s network and servers enables the threat actor to monitor communications, track user activities, and gather intelligence for espionage purposes.
Ransomware Deployment: The threat actor may deploy ransomware attacks on the company’s systems, encrypting critical data and demanding payment for decryption keys.
Data Manipulation: By gaining access to the company’s servers, the threat actor can modify or delete data, leading to potential disruptions in operations or reputational damage.
Credential Theft: With direct credentials access, the threat actor can steal login credentials of employees, administrators, or students, leading to further compromise of other systems or accounts.
Network Exploitation: The threat actor can leverage the compromised access to launch attacks on other entities connected to the company’s network, potentially expanding the scope of the breach.
Overall, the unauthorized access poses a significant threat to the confidentiality, integrity, and availability of the company’s data and infrastructure, potentially resulting in financial losses, regulatory violations, and damage to reputation.